One of the oldest scams around — the fake job interview that seeks only to harvest your personal and financial data — is on the rise, the FBI warns. Here’s the story of a recent LinkedIn impersonation scam that led to more than 100 people getting duped, and one almost-victim who decided the job offer was too-good-to-be-true.
Last week, someone began began posting classified notices on LinkedIn for different design consulting jobs at Geosyntec Consultants, an environmental engineering firm based in the Washington, D.C. area. Those who responded were told their application for employment was being reviewed and that they should email Troy Gwin — Geosyntec’s senior recruiter — immediately to arrange a screening interview.
Gwin contacted KrebsOnSecurity after hearing from job seekers trying to verify the ad, which urged respondents to email Gwin at a Gmail address that was not his. Gwin said LinkedIn told him roughly 100 people applied before the phony ads were removed for abusing the company’s terms of service.
“The endgame was to offer a job based on successful completion of background check which obviously requires entering personal information,” Gwin said. “Almost 100 people applied. I feel horrible about this. These people were really excited about this ‘opportunity’.”
Erica Siegel was particularly excited about the possibility of working in a creative director role she interviewed for at the fake Geosyntec. Siegel said her specialty — helping wealthy people develop their own personal brands — has been in low demand throughout the pandemic, so she’s applied to dozens of jobs and freelance gigs over the past few months.
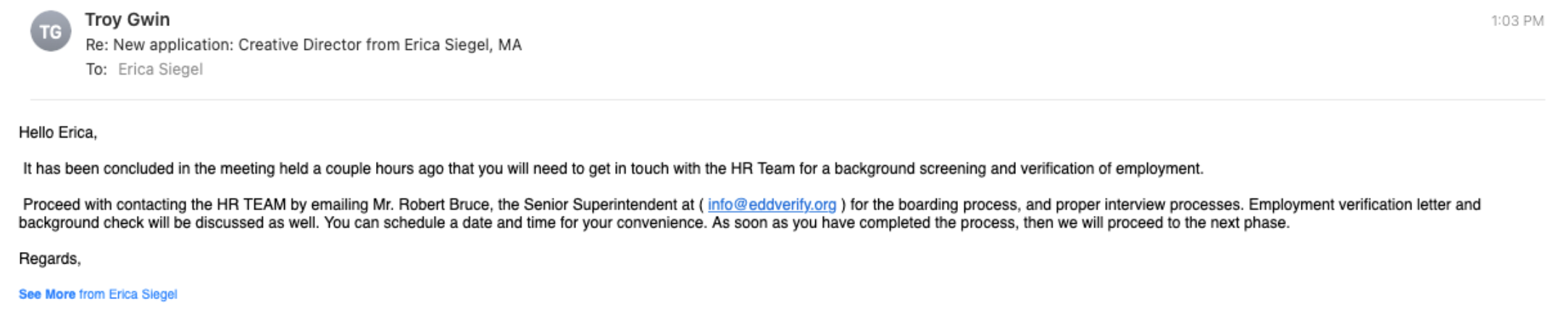
On Monday, someone claiming to work with Gwin contacted Siegel and asked her to set up an online interview with Geosyntec. Siegel said the “recruiter” sent her a list of screening questions that all seemed relevant to the position being advertised.
Siegel said that within about an hour of submitting her answers, she received a reply saying the company’s board had unanimously approved her as a new hire, with an incredibly generous salary considering she had to do next to no work to get a job she could do from home.
Worried that her potential new dream job might be too-good-to-be-true, she sent the recruiter a list of her own questions that she had about the role and its position within the company.
But the recruiter completely ignored Siegel’s follow-up questions, instead sending a reply that urged her to get in touch with a contact in human resources to immediately begin the process of formalizing her employment. Which of course involves handing over one’s personal (driver’s license info) and financial details for direct deposit.
Multiple things about this job offer didn’t smell right to Siegel.
“I usually have six or seven interviews before getting a job,” Siegel said. “Hardly ever in my lifetime have I seen a role that flexible, completely remote and paid the kind of money I would ask for. You never get all three of those things.”
So she called her dad, an environmental attorney who happens to know and have worked with people at the real Geosyntec Consultants. Then she got in touch with the real Troy Gwin, who confirmed her suspicions that the whole thing was a scam.
“Even after the real Troy said they’d gotten these [LinkedIn] ads shut down, this guy was still emailing me asking for my HR information,” Siegel said. “So my dad said, ‘Troll him back, and tell him you want a signing bonus via money order.’ I was like, okay, what’s the worst that could happen? I never heard from him again.”
HOW TO SPOT A JOB SCAM
In late April, the FBI warned that technology is making these scams easier and more lucrative for fraudsters, who are particularly fond of impersonating recruiters.
“Fake Job or Employment Scams occur when criminal actors deceive victims into believing they have a job or a potential job,” the FBI warned. “Criminals leverage their position as “employers” to persuade victims to provide them with personally identifiable information (PII), become unwitting money mules, or to send them money.”
Last year, some 16,012 people reported being victims of employment scams with losses totaling more than $59 million, according to the FBI’s Internet Crime Complaint Center (IC3). But the real losses each year from employment scams are likely far higher; as the Justice Department often points out, relatively few victims of these crimes report the matter to the IC3.
LinkedIn said its platform uses automated and manual defenses to detect and address fake accounts or fraudulent payments.
“Any accounts or job posts that violate our policies are blocked from the site,” LinkedIn said in response to a request for comment. “The majority of fake job postings are stopped before going live on our site, and for those job postings that aren’t, whenever we find fake posts, we work to remove it quickly.”
LinkedIn’s most recent transparency report says these automated defenses block or automatically remove 98.4% of the fake accounts. But the scam that ensnared Gwin and Siegel is more of a hybrid, in that the majority of it operates outside of LinkedIn’s control via email services like Gmail and Yahoo.
This, by the way, should be a major red flag for anyone searching for a job, says the FBI: “Potential employers contact victims through non-company email domains and teleconference applications.”
Here are some other telltale signs of a job scam, as per the FBI:
-Interviews are not conducted in-person or through a secure video call.
-Potential employers contact victims through non-company email domains and teleconference applications.
-Potential employers require employees to purchase start-up equipment from the company.
-Potential employers require employees to pay upfront for background investigations or screenings.
-Potential employers request credit card information.
-Potential employers send an employment contract to physically sign asking for PII.
-Job postings appear on job boards, but not on the companies’ websites.
-Recruiters or managers do not have profiles on the job board, or the profiles do not seem to fit their roles.
from Krebs on Security https://ift.tt/3bMGEdz